Enterprise businesses are too big to rely on copper-wire telephone service anymore, so they use the cloud as a platform for their voice systems. Cloud, however, seems to still be regarded as an amorphous term in 2016, so let’s provide some simplified definitions around key terms regarding cloud communications and clear the air.
VOIP, CLOUD COMMUNICATIONS, BUSINESS
5 Benefits Cloud Communications Brings to Business
When enterprise businesses search for a voice solution, a complete cloud communications solution is frequently presented as an option.
KazooCon 2016 agenda!
We’re so excited to officially announce sponsors and the agenda for KazooCon 2016. The event will be hosted on October 17th – 18th at Broadway Studios in San Francisco, CA. Inspired by Kazoo’s VoIP open-source platform and hosted by 2600Hz, KazooCon brings together developers, managed service providers, carriers and telecom evangelists to create unified communications systems.
Building Your Brand - Why White Labeling is So Important
Imagine this: You’re on the phone with a customer, nailing down your VoIP deal, when you say, “Alright, I’ll set you up in the XYZ user portal and you’ll be good to go!.” The customer responds, “XYZ? What’s that? You don’t make your own products?”
Bypass Media Mode
How is media handled?
When we talk about media, we are talking about the audio packets going to and from an endpoint, where an endpoint could be your desk phone, fax machine, an upstream carrier, etc.
Let's assume you're calling a number not managed by the Kazoo installation.
How Collaboration Propels the Landscape of Enterprise Voice
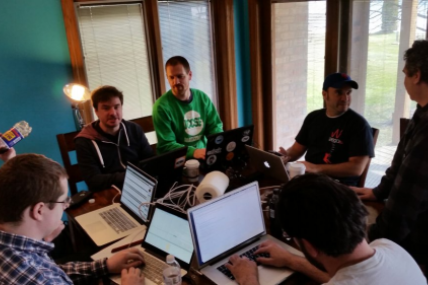
When we gather for KazooCon 2016 on October 17 & 18, we, as a community of voice resellers, do more than just network and evangelize our products. Together we solve problems and bring about change to the business voice industry. Collaboration is one of the single most powerful actions we can take.
2600Hz speaks with Nexmo CEO Tony Jamous
Nexmo operates a cloud communications platform that develops APIs for SMS, voice, and phone verifications. In June 2016, Vonage acquired Nexmo, positioning the combined company as a best-in-class leader across the two dominant modes of communication today – voice and messaging.
25 Days to KazooCon 2016!
Learn about our Kazoo 4.0 Release and much more at KazooCon 2016! Only 10 more days until Early Bird Pricing ends!
Want to learn more? Check out What to Expect at KazooCon 2016.
What To Expect at KazooCon 2016
KazooCon is about the communications revolution, and this year we’re introducing the voice advances that enterprises have been waiting on.
40 Days to KazooCon 2016!
Only 40 days to KazooCon 2016, and Super Early Bird Tickets are expiring this Friday 9/9!
Announcing KazooCon 2016
We are thrilled to announce that our 4th Annual KazooCon is happening October 17th-18th in beautiful San Francisco, California.
HOW TO FIND THE BEST TRUE VOIP PBX SYSTEM
In our previous blog post, we discussed what it means to be “True Cloud.” But how do you know when the platform you are using is True Cloud? How do you know which “cloud” to trust?
True Cloud - Let’s talk about it
As industries have shifted to “Cloud” technologies, it has become even more important to dive deeper and ascertain what companies mean when they boast about “Cloud Technology.”
Top 4 Business Benefits of Becoming a VoIP Reseller
1. GROW YOUR BRAND
With a white-label provider, you can sell VoIP services under your own brand. This allows you to sell the services as though they are your own, without actually having to invest the time and money into building your own platform.
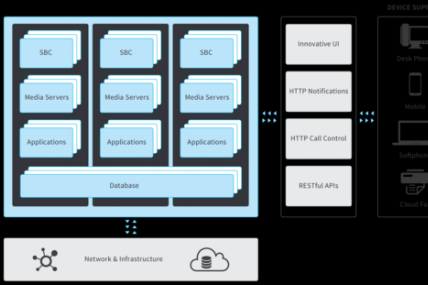
Working with FreeSWITCH as a core part of Kazoo
Today, the core architects of the Kazoo platform are in Milwaukee, WI working with the amazing FreeSWITCH team. The FreeSWITCH team runs an awesome open-source project that is on the bleeding edge of communications - always.
2600Hz Announces Full Integration with Innovative new “Carrier Pigeon” service.
San Francisco, CA - April 1st, 2016 - With skyrocketing demand for integrations between different services, 2600Hz is staying ahead of the competition with a unique integration named “Carrier Pigeons”.
Introducing the Next Generation of 2600Hz
You may have noticed our shiny new website, featuring our new 2600Hz brand.
This is the new generation of 2600Hz, and we are so excited to share it with you.
Kazoo’s First Independent International Community Conference - Moscow 2015
Open-Source is an enormous component of what powers 2600Hz. Not only are we supporting and contributing to other open-source projects, the Kazoo platform is open-source.
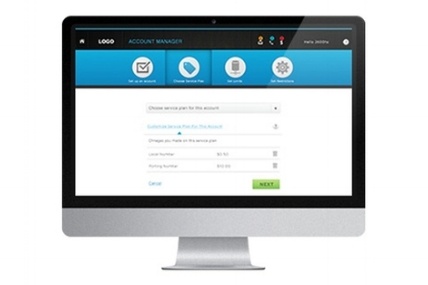
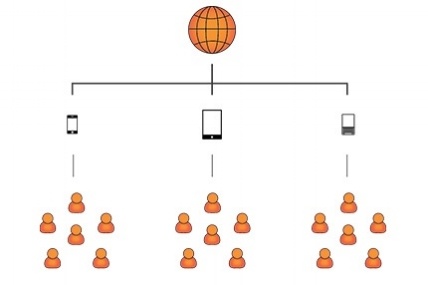
Accounts Manager - Infinite VoIP Account Scalability and Control
The Accounts Manager App is a dynamic web portal providing multi-tenant functionality for worry-free scaling. Manage all of your accounts, and provide granular control to ensure customers have an enjoyable experience.
PRODUCT NEWS, TECHNICAL, COMPANY
Tuning Kazoo to 10,000 Handsets - KazooCon 2015
People love to talk about scale. Some vendors pitch that their systems easily support 100,000 simultaneous calls, or 500 calls per second, etc. The reality is, in the real world, people’s behaviors vary and the feature sets they use can cut these numbers down quickly.
VirtualPBX - Back Office, Delivering Voice in a Competitive Market - KazooCon 2015
In a competitive market, high quality voice services alone are rarely enough. Lon Baker speaks about the customer lifecycle, back office systems from Sales to CRM to deployment, and how to drive profitable growth while delivering an excellent customer experience.
Telnexus - Quote to Cash – KazooCon 2015
Telnexus CEO Vernon Keenan discuss how he built the Managed Service Provider Telnexus from the ground up and the lessons he has learned in the process.
SIPLABS - Hard Rocking Kazoo - KazooCon 2015
Founder and CEO Mikhail Rodionov discusses all the projects and code contributions that they have built for Kazoo over the past year.
ThinQ - Least Cost Routing in the Cloud - KazooCon 2015
The team at ThinQ show how to set up your routing profile, carrier selection, high volume traffic management, and LCR routing.
Billing Data with Kazoo - KazooCon 2015
Product Director Aaron Gunn discusses billing options for SaaS and IaaS customers. This includes CDR API, AMPQ, and integrating VoIP billing platforms.
ARCHIVES, PRODUCT NEWS, TECHNICAL, COMPANY
The Next Wave - KazooCon 2015
CTO Karl Anderson discusses the state of Kazoo. This includes integrations with FreeSWITCH, erlang, and Kamailio. Reseller milestones include the release of whitelabeling, webhooks, migration, carriers, debugging, account management and more.
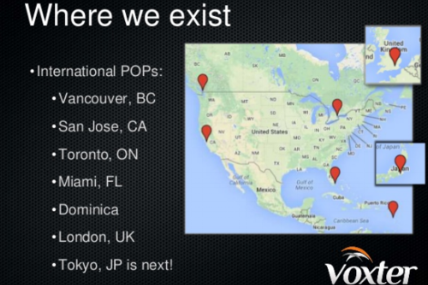
Voxter - Building Value with Kazoo - KazooCon 2015
The Voxter team discuss code contributions to the Kazoo platform, discuss how they are utilizing the platform, and give an in-depth demo of WhApps.
Kamailio and VoIP Wild World
Daniel Constantin Mierla discusses Kamailio and Kazoo integrations at KazooCon.
Detecting and Managing VoIP Fraud (Slides) - KazooCon 2015
This is an overview of VoIP fraud, different types of fraud and what telecommunication carriers are doing to combat this issue.
ARCHIVES, PRODUCT NEWS, COMPANY, BUSINESS
Detecting and Managing VoIP Fraud - KazooCon 2015
This is an overview of VoIP fraud, different types of fraud and what telecommunication carriers are doing to combat this issue.
ARCHIVES, PRODUCT NEWS, COMPANY
Telecom Rating and Limits - KazooCon 2015
Read MoreSmartPBX: At the Intersection of Simplicity and Functionality
The SmartPBX App combines comprehensive PBX functionality with user-friendly interface. Set up new users in minutes, manage all of your accounts, reduce installation and labor costs, and provide business-specific user features. All services are controlled via API’s, allowing you to extend the App functionality as needed. Within the interface you have the ability to create, manage, and remove...
Top Ten Reasons Why I’m Going to KazooCon!
We’re slightly more than 20 days away from KazooCon 2015 and we want you here to see the power and scalability of our new VoIP platform firsthand. So if you are still on the fence on attending, we’re revealing the top ten reasons why you need to attend the Unified Communications Revolution. Early-bird pricing ends on Sunday, September 20th, so register now and save money. So what are you waiting...
ARCHIVES, PRODUCT NEWS, COMPANY
Kazoo Release Notes v3.21
PRODUCT/ FEATURE IMPROVEMENTS
It is hard to stress how exciting this version release is for our resellers, who are passionate about the end user experience. Some of the requests came through our community, who helped us beta test before launch, and deserve a hand for kicking the tires! Some major highlights:
ARCHIVES, PRODUCT NEWS, CUSTOMER, BUSINESS
2600Hz Case Study: A Look At Slable’s Partnership and How 2600Hz’s Offerings Improved Their Business
About Slable
Slable provides affordable enterprise I.T. and communication solutions for small-to-medium businesses (SMB) in the Washington, D.C. metropolitan area.
Kazoo at scale, and supporting WebRTC and Mobile
SendHub co-founder Ryan Pfeffer discusses a product overview, Kazoo at scale, and supporting WebRTC and Mobile.
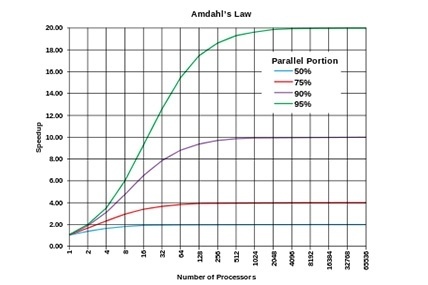
Amdahl's Law & Parallel Computing
We talked a lot about the various computing power laws in a previous blog post, but one of the themes was the ascent of parallelization in code.
Bezos Law
COMPUTING OVER TIME
When we think about advances in computing power, most people think of Moore’s Law, Kryder’s Law, or Nielsen’s law, which are about the pace of technical development. Moore’s law is the most well known, and talks about the pace of computational intensity doubling every 18-24 months.
How Squirrels Break DataCenters And Other Database Conjectures
This Q&A presentation was influenced by Kyle Kingsbury’s work on Jepsen, an exploration of modern databases. If you haven’t seen his work and you like this stuff, you should go check it out. It’s awesome.
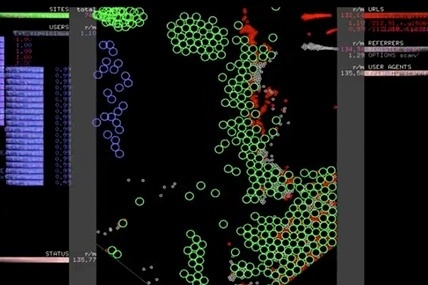
Visualizing A Cyber Attack
Visualizing a Cyber Attack on a VoIP server. Really cool visualization!
The best part is that the honeypot (the server setup by the security researchers) is not even broadcast to the public internet as a VoIP server. Imagine the scale of attacks advertised servers receive.
Voice Isn't Dying
It seems like everywhere you look these days, someone is killing the voice network. ReadWriteWeb says “Microsoft’s Skype owns 1/3rd of a dying network” and Facebook has amobile client that now does free phone calls, but all of these projects are missing the point.
TECHNOLOGY, COMMUNICATIONS, STARTUPS, ARCHIVES, DPI, DEEP PACKET INSPECTION, VOIP, ITU, TECH, TECHNICAL
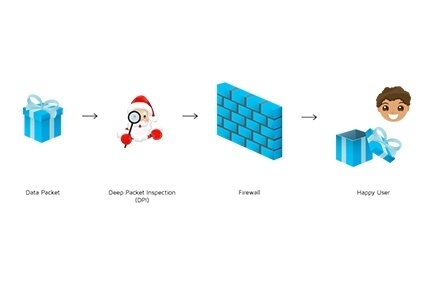
To Have or Have Not: DPI, the ITU and What it Means TO YOU
Ho Ho Ho! It’s time for the holidays around these parts but things aren’t quite as silent as one might hope. Thanks to a big holiday present from the International Telecom Union (ITU) the whole world is watching as operators drink eggnog and debate the free world as we know it.
COMMUNICATIONS, ARCHIVES, TECHNICAL
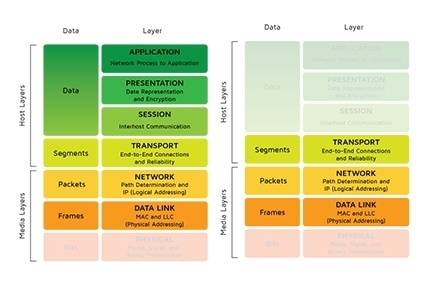
The Difference Between a Firewall and an SBC
Firewalls or SBC’s? What’s the difference to you and me?
Seems like this question comes up a lot in our business. Controlling access to a site is critically important for most enterprises and the most common way to enforce policies is a firewall.
DISASTER, RECOVERY, COMMUNICATIONS, ARCHIVES, BUSINESS
Part 2 of our Disaster Recovery Series
“If you’re going through Hell, Keep Going”-Winston Churchill
Winston Churchill had it right when he talked about perseverance. When things look grim, it’s time to double down and make things right. Today we’re talking about Disaster Recovery: how you can stay online even when the streets look like a scene from I am Legend.COMMUNICATIONS, ARCHIVES, BUSINESS
BYOD vs CYOD
BYOD Versus CYOD: User Choice in a Policy Driven World
Humans crave freedom, but is freedom of choice practical in the Enterprise World? Since the iPhone launched in 2007, there’s been a remarkable trend.